How to Create Cloud-Ready Environments with Azure Landing Zones
As businesses set their sights on building an IT environment that’s agile, scalable and cost-efficient, achieving digital transformation in the cloud is a vital destination on their roadmap.
Azure landing zones are an integral part and the first step for any business looking to build a cloud-based environment and migrate their workloads. They give you unified control and ensure seamless operations on a daily basis. For this reason and more, designing and implementing landing zones has become an important aspect in the migration phase of a business’s digital transformation journey in the cloud.
In this blog post, we provide a detailed, step-by-step approach on how to strategize, design and implement landing zones in Azure.
Key Objectives and Outcomes for Designing Landing Zones
When designing and strategizing an effective landing zone, Navisite sets out to achieve the following key objectives and outcomes to ensure maximum effectiveness in the cloud:
- Ensure tighter security control over the infrastructure and application workloads from both external and internal threats
- Full visibility of user activities
- Pre-defined customer compliance policies embedded across all the workloads
- All workloads’ resources to be grouped appropriately according to their application-type/environment or other factors in concurrence with customer requirements
- Provision to monitor and control overall cloud spend
- Adherence to customer compliance and audit policies
- Enhanced flexibility for internal IT teams to manage workloads
Design Principles to Consider for Landing Zone Implementation
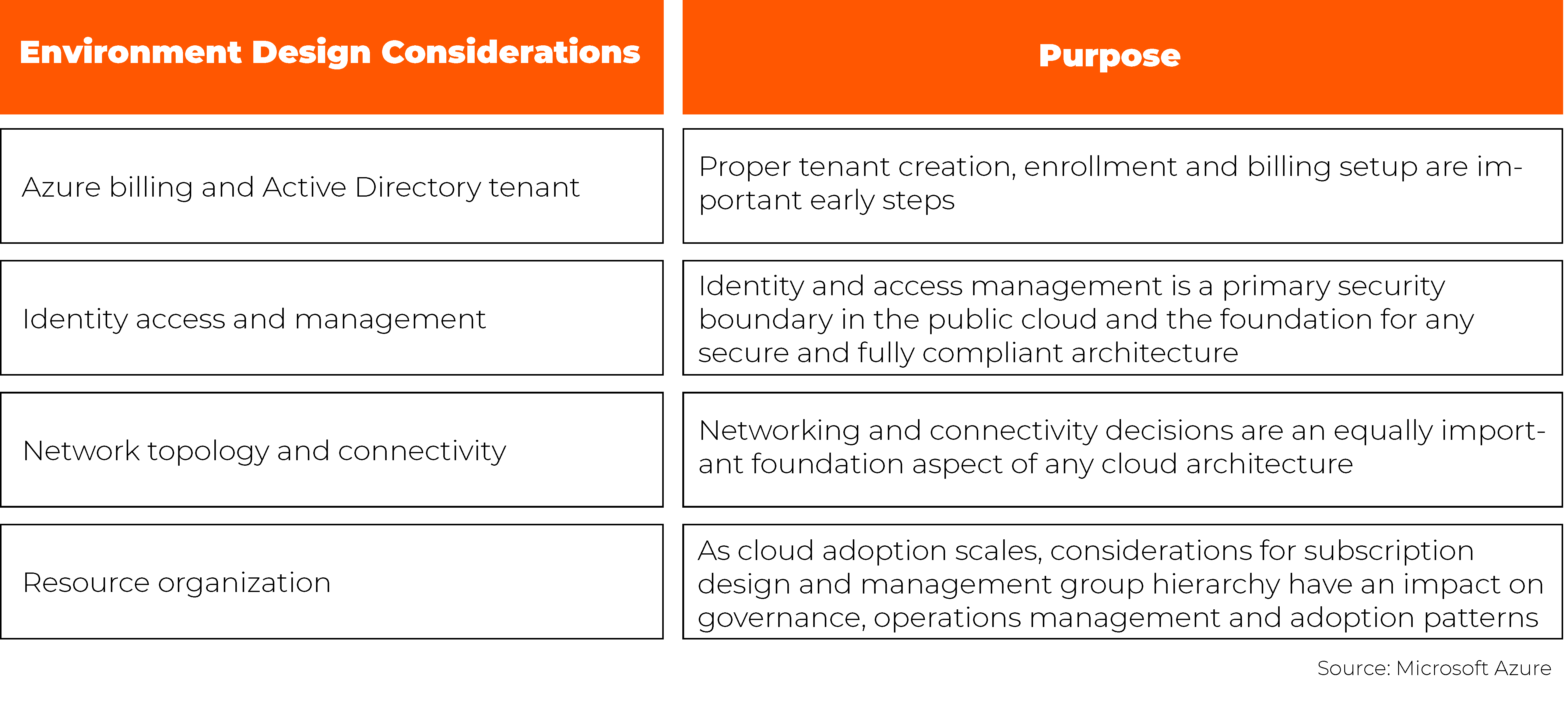
Before implementing a landing zone, one of the key first steps is to first consider your deployment approach and defined design principle. There are two design areas to consider: environment and compliance. Navisite evaluates each of these areas to design a landing zone that’s unique to a business’s environment and needs.
Environment Design
This environment design helps in identifying foundational elements that underlay the security and governance principles of businesses. Here are the key design areas to consider:
Compliance Design
This compliance design helps in ensuring the smooth operation and management of workloads. This includes the selection of appropriate tools and services in adherence to compliance policies. With deep experience across all industries, Navisite can also help businesses adopt the right best practices to ensure full compliance. Here are the key design areas to consider:
Designing Your Landing Zone Architecture
Navisite factors the core design principles defined in the Microsoft Azure Cloud Adoption Framework (CAF) and provides a standard unified approach in the implementation of the landing zone for its customers. Navisite encourages custom modifications based on a business’s requirements without much deviation from the underlying design principles mentioned in the sections above.
Network Architecture Design
The design of Azure networking architecture is a critical part of the cloud adoption journey, as it ensures workloads and services are properly supported in the cloud and helps businesses prepare for the landing zone implementation. A key step here is assessing applications and services to determine their network connectivity requirements. For each application or service, the following decision tree can help you determine the networking tools or services to use:
Source: Microsoft Azure
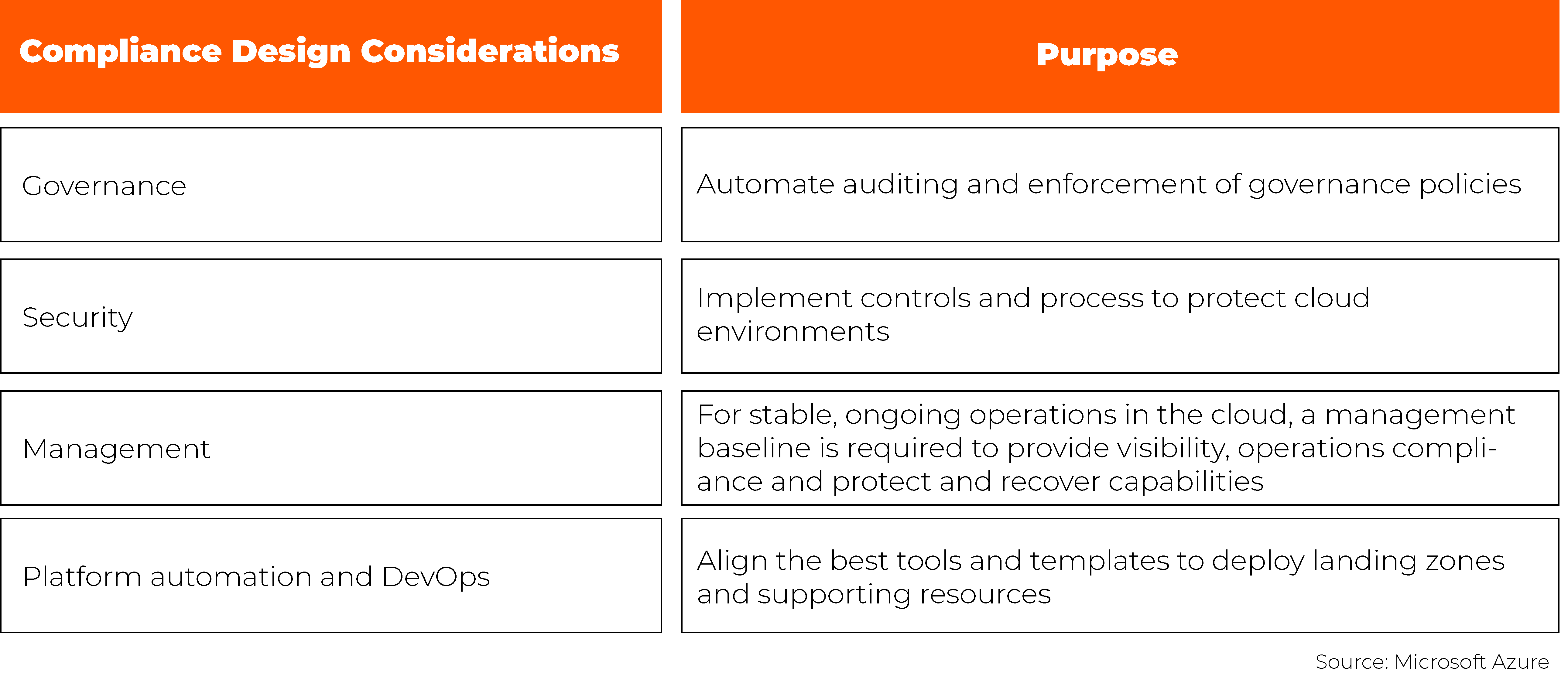
In most migration scenarios, Navisite recommends the hub and spoke topology model, with all common components residing at the hub virtual network and different environments (like development, stage, or production) inside the spoke virtual network. All network traffic is routed by the hub where Azure application gateways, Azure virtual network gateway, Azure firewall, Azure virtual WAN or NVA are deployed to inspect and serve the traffic going in and out from the business’s tenant.
Spokes should have different subnets like web, app and database, which are protected by the network security group (NSG) configuration. Each business and their requirements are different, which can change the architecture. Below are some of the examples of landing zone designs that Navisite usually recommends.
Based on the network reference architecture and design considerations mentioned above, Navisite follows a standard and more generic high-level landing zone architecture design:
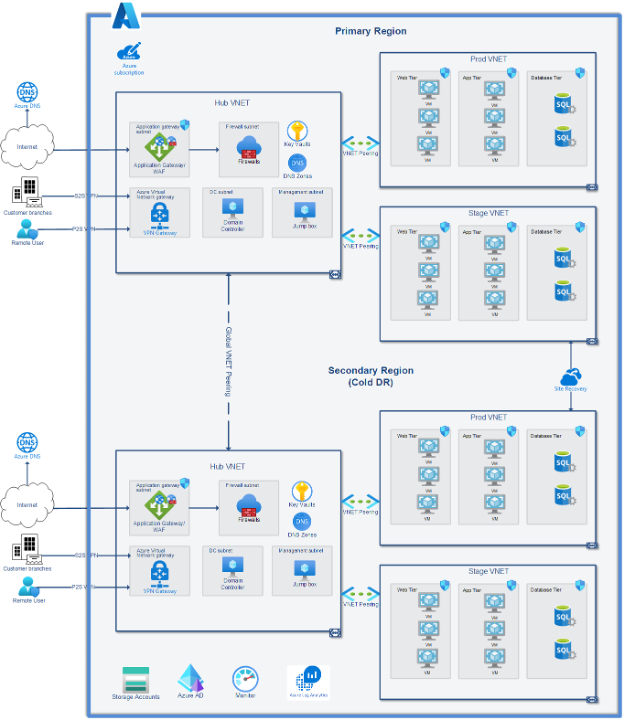
Resource Hierarchy
Azure provides four levels of management scope:
- Management groups
- Subscriptions
- Resource groups
- Resources
Source: Microsoft Azure
All resources, whether virtual machines, database servers, app services or network components, are deployed in their own resource groups, which provide the specific segregation and billing. In other words, resource groups are like containers, having similar services to manage. These groups offer features like access control, locks and tags to secure and organize resources after deployment.
Deployment Options
Azure supports the automation to deploy the complete landing zone, and this becomes very important when the business’s environment is continuously growing at a rapid rate. This ensures infrastructure is set up to evolve and scale as use-cases expand and demands grow. Source control allows for traceability of changes to the code and automated testing ensures that new changes match security policies. Navisite uses tools like Terraform or Azure ARM templates to deploy all of the above resources in a fast-paced manner during Azure migrations.
Identity and Access Management
Managing the security of your IT environment is becoming increasingly difficult as threats like password spray, replay and phishing become more common. Navisite follows security defaults as outlined by the Microsoft Security best practices, which make it easier to protect businesses from these attacks with pre-configured security settings, including:
- Require all users to register for Azure AD Multi-Factor Authentication
- Require administrators to do multi-factor authentication
- Block legacy authentication protocols
- Require users to do multi-factor authentication when necessary
- Protect privileged activities like access to the Azure portal
Navisite also uses Azure CSP and Lighthouse to provide granular access to support staff.
Azure Resource Tagging
Naming and tagging standards for all the resources deployed in Azure make it easier to organize and manage cloud-based resources. Some tagging examples include:
- Resource management
- Cost management and optimization
- Operations management
- Security
- Governance and regulatory compliance
- Automation
- Workload optimization
Navisite follows a strong naming convention process by deploying every resource with customer code, which acts as a reference for support staff to provide the best monitoring and management standards.
Learn more about Navisite’s Azure capabilities and how our team can help you manage and monitor cloud deployments.